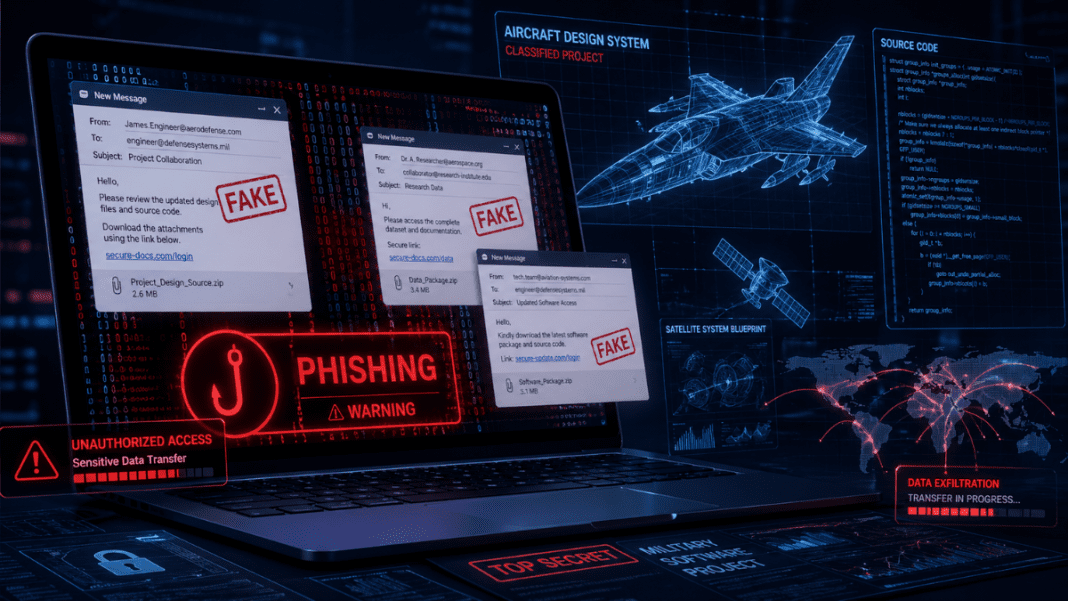
A major phishing and cyber-espionage operation has been uncovered involving a long-running phishing campaign that targeted sensitive aerospace and military technology. Investigators from the NASA Office of Inspector General revealed that the scheme lasted for several years, from 2017 to 2021.
During this time, a cybercriminal identified as Song Wu carried out a carefully planned deception. The attacker posed as trusted professionals, including engineers and academics, to gain access to restricted software. These tools were not ordinary programs. They were used in the design of aircraft and advanced military systems.
The operation affected multiple high-profile institutions. These included NASA, branches of the U.S. military such as the Air Force, Navy, and Army, as well as the Federal Aviation Administration (FAA). Universities and private aerospace companies were also targeted.
The phishing campaign did not rely on traditional hacking methods. Instead, it focused on human interaction. By creating fake identities and building trust, the attacker convinced victims to share sensitive information willingly.
How the Phishing Operation Worked
The cybercriminal used a method known as impersonation phishing. This involves pretending to be someone else to trick people into sharing confidential data. In this case, fake email accounts were created to resemble those of well-known aerospace experts.
Operational blunder exposes massive Russian cyber espionage attack on Ukrainian prosecutors
Messages were sent to professionals working in sensitive fields. These emails appeared genuine and often included technical language to build credibility. Victims believed they were communicating with legitimate colleagues or collaborators. This type of phishing attack relied on trust rather than technical hacking.
In many cases, the attacker requested access to restricted software or even its source code. Source code is highly valuable because it reveals how a program works in detail. Sharing such information can lead to serious security risks.
Some warning signs were present but not always noticed. These included repeated requests without clear reasons, unusual ways of handling payments, and sudden changes in communication patterns. Despite these signs, several individuals unknowingly shared protected data.
The information obtained was linked to tools used in designing aircraft and military systems. Such technology is controlled under strict export regulations. These rules are designed to prevent sensitive data from being transferred to foreign entities without permission.
By tricking victims into sharing this information, the attacker bypassed these controls. This made the operation especially concerning for national security.
Investigation and Legal Charges
The case was investigated jointly by the NASA Office of Inspector General and the Federal Bureau of Investigation. Their findings revealed the full scale of the operation and the methods used.
DeFi giant Drift Protocol loses nearly half of total value locked in coordinated cyberattack
Authorities discovered that dozens of professionals had been contacted over the four-year period. These included employees from government agencies, researchers, and industry experts. The attacker’s strategy relied on patience and persistence, gradually building trust with targets.
As a result of the investigation, multiple criminal charges were filed against Song Wu. These include counts of wire fraud and aggravated identity theft. Each wire fraud charge carries a significant prison sentence, and additional penalties apply for identity theft.
Despite the charges, Song Wu has not yet been taken into custody. A federal arrest warrant has been issued, and the individual remains at large.
The case highlights a growing concern in the scientific and technological community. Phishing attacks are becoming more advanced and harder to detect. They no longer rely on obvious scams but instead use detailed knowledge and careful planning.
According to officials, including Ryan Pittman, this incident reflects a broader pattern of threats targeting sensitive technology. Over the past decade, the NASA Office of Inspector General has opened more than 80 investigations related to export control violations. These cases have resulted in millions of dollars in economic impact.
The findings emphasize the risks faced by organizations handling sensitive technology. Even routine communication, such as email exchanges, can become a point of vulnerability if not handled carefully.
The exposure of this multi-year phishing plot shows how cybercriminals can exploit trust to gain access to critical information.