A Russian hacking group has been caught pretending to be a famous cybersecurity company.
Russian Hackers Use Fake Cyber Firm to Target Embassies
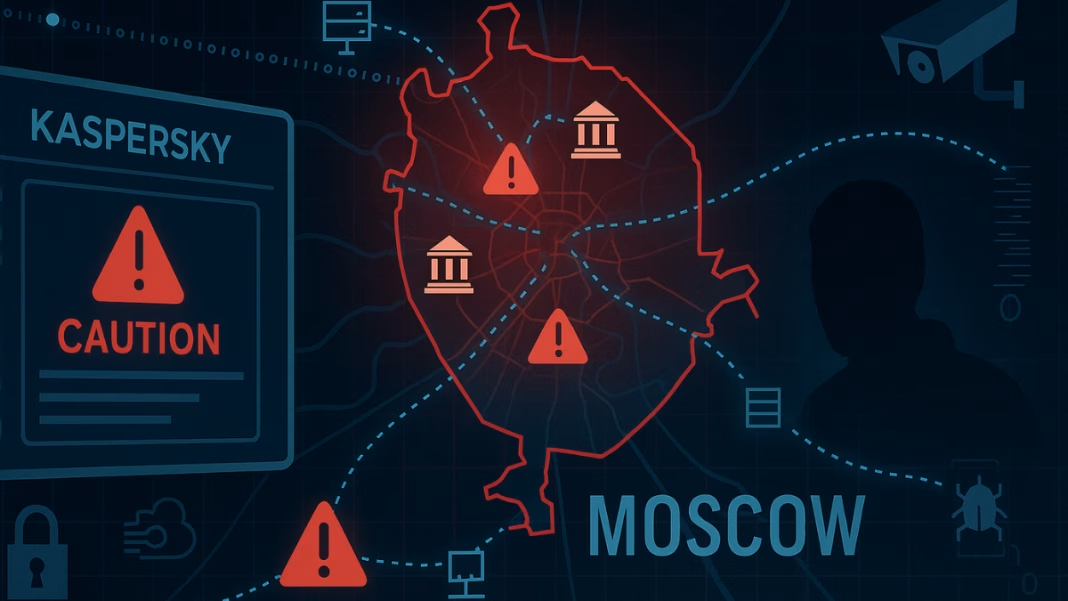
According to a recent report by Microsoft, this group secretly attacked foreign embassies in Moscow by using fake software that looked like it came from the Russian company Kaspersky.
The hackers belong to a group known as Turla, also called Secret Blizzard. Experts believe Russia’s intelligence agency employs them. They have carried out cyberattacks for more than 25 years and rank among the most advanced and sneaky hacker groups in the world.
In this cyberattack, Turla used Russian internet service providers (ISPs) to launch the hack. These are the same networks that regular people in Russia use. This helped the hackers hide. They secretly watched what foreign diplomats were doing online. Then, they stole their information.
Microsoft says the hackers acted like they were cybersecurity experts. They made their harmful software look like Kaspersky’s antivirus tools. This trick helped them stay hidden. The people they were spying on didn’t notice. The malware they used is called ApolloShadow.
Spying Through the Internet with ApolloShadow Malware
The malware, ApolloShadow, is a powerful spying tool. Once it is placed inside a computer, it removes the safety features that protect personal information online. It turns secure data into readable text that hackers can easily understand.
For example, it can reveal a person’s internet browsing habits, login usernames, and passwords. This is a serious threat because it can expose sensitive government information. Since many embassies were targeted, it’s likely that private diplomatic conversations and official data may have been stolen.
The report says the hackers used Russian ISPs to send the malware to embassies. This let them secretly control internet traffic. They tricked embassy computers. The computers thought they were downloading safe software from a trusted company. But they were actually downloading malware.
Microsoft said this was a “large-scale” operation. They did not name the embassies they attacked, but they located all of them in Moscow. Because the malware looked like it came from Kaspersky, many users may not have suspected anything unusual.
Kaspersky responded by saying that trusted companies are often misused in cyber scams. They warned people to only download apps from official websites and to always double-check who sent any messages or software.
📜 Quiet Towns, Loud Secrets—Brazil Became Ground Zero for Russian Espionage
Russian Surveillance System Helps Cyber Attacks
Russian law permits SORM and allows law enforcement to monitor people’s digital activity. But in this case, it may have also enabled the hackers to carry out their spying without getting caught. By working with ISPs and using systems like SORM, the hackers had a clear path to carry out their attacks inside Russia.
This incident comes at a time when global tensions with Russia are already very high. Russia’s ongoing war and its growing control over the internet have made many countries more worried about cybersecurity threats.
The U.S. had earlier banned the use of Kaspersky’s products due to national security concerns. Authorities feared that the Russian government could influence the company. Now, this latest hacking case adds more fuel to those concerns, especially since the hackers used fake Kaspersky software to carry out their mission.
The Russian government has not answered these claims. Microsoft said the attack was carefully planned. The goal was to steal important information. The hackers used powerful tools. They also had access like a government would. This helped them break into some of the world’s most secure systems.