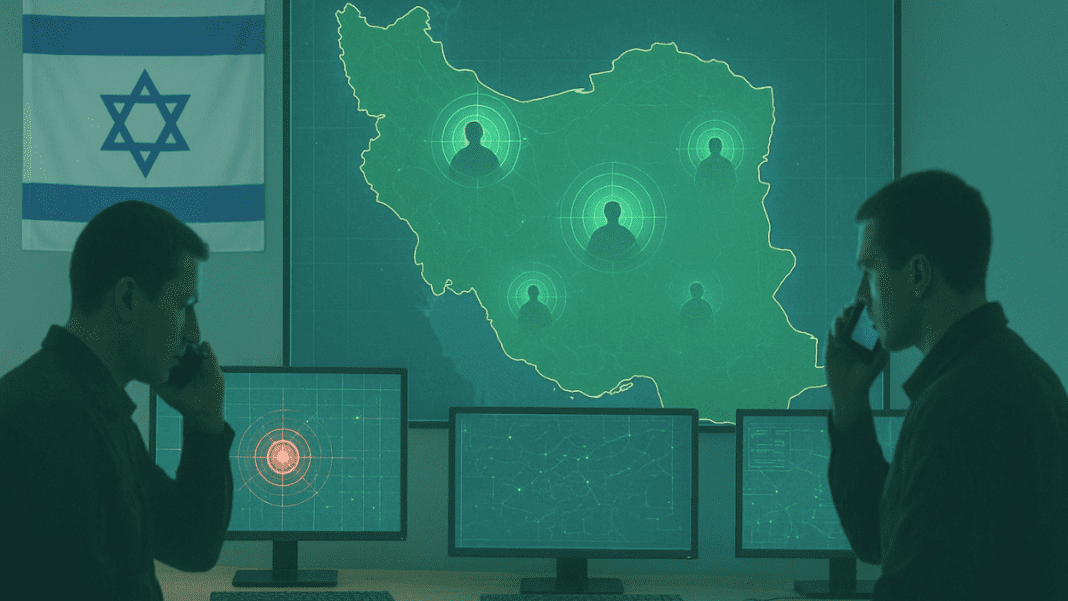
A new report has revealed how Israel managed to target senior Iranian leaders during the June conflict by exploiting a simple weakness — mobile phones carried by bodyguards and drivers.
Phones Became Israel’s Tracking Tool
According to officials, top political and military leaders avoided using cell phones themselves, knowing they could be traced. But their security teams, assistants, and drivers did not follow the same rules. Many of them carried personal phones and even used them for social media during the war.
This mistake gave Israel a powerful advantage. By hacking into those devices, Israeli intelligence was able to monitor the movements of some of Iran’s most senior officials and scientists. Officials explained that while leaders avoided direct exposure, the constant presence of armed escorts and staff with phones created digital trails that were easy to follow.
The reliance on phones by guards and aides turned out to be the biggest vulnerability. Despite Iran increasing security measures once it learned of possible attacks, the use of these devices still opened doors for Israel to locate and strike key figures.
Israel’s Decapitation Plan at Start of War
The report describes that Israel had prepared a strategy to weaken Iran’s leadership from the very beginning of the 12-day conflict, which started on June 13. The plan focused on striking top commanders and decision-makers before they could coordinate defenses after the surprise assault.
In one of the first operations, Israeli forces tracked a high-ranking commander. He had gathered senior staff for an emergency meeting. Soon after, the meeting place was bombed. The strike killed him and his team. Israeli defense officials said this was possible because they traced digital signals from the phones of people around him.
How Cyber Attacks on Industrial Control Systems Can Endanger Lives ?
The attacks were designed to destabilize Iran’s command structure at the outset of the war. Israeli sources admitted that the unusually large number of bodyguards and staff members surrounding top figures worked in their favor. Every phone in the vicinity provided another possible route for monitoring.
“Using so many guards is a weakness we could exploit,” one official said. Israel viewed the massive security presence not as a barrier, but as a digital footprint that revealed exact locations.
Mistakes Continued Despite New Rules
Iranian security teams received orders to stop using mobile phones near officials after the early strikes. They began relying on walkie-talkies, and only team leaders carried communication devices. Commanders instructed these leaders not to travel directly with high-profile figures.
The strict rules were not always followed. In one incident, a group of guards ignored the order. They kept using their cell phones. This mistake allowed Israel to trace a meeting of senior political leaders. But in that case, the strike missed the intended targets.
Kristi Noem fires FEMA’s 24 IT staff after massive cybersecurity breach
Israel fought the June war for nearly two weeks and launched heavy attacks on Iran’s leadership, nuclear scientists, missile program, and uranium enrichment sites. Israeli officials said the strikes were necessary to prevent Iran from advancing plans to harm their country.